Hope you guys are doing well since it’s been a long I haven’t shared anything because of some personal issues and stuff, even though it ain’t much of research, just wanted to share for the infosec community.
All this happened when I saw a program on a Bugcrowd with very limited scope even though wildcard domains were not in scope, still gave a try to correlate the stuff.
While scrolling through the subdomains, something caught my attention.
Ngrok is a cross-platform application that enables developers to expose a local development server to the Internet with minimal effort most organizations use the Ngrok service to make their local server available on the internet temporarily since Ngrok service is easy to deploy and use which makes it the first choice.
It seemed like a potential Ngrok subdomain takeover but cannot say anything without verifying manually. So I signed up for the Ngrok service and tried to create a subdomain with xxxx-xxxx.eu subdomain name but got to know that the tunnel name is unavailable. WAIT, that was a mistaken attempt actually i had to choose the region and use xxxx-xxxx only where .eu will be appended automatically, after choosing the region i.e Europe (EU), and finally was able to create the subdomain name to which the vulnerable subdomain was pointed also I had to subscribe to the basic plan in order to create a custom subdomain.
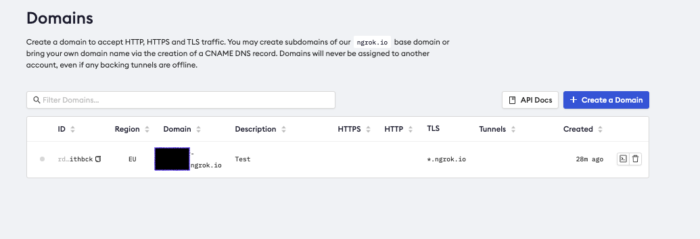
After setting up Ngrok in the device and configuring the auth token, it was time to share the localhost.
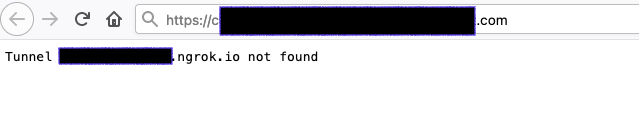
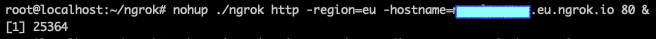
ngrok http -region=eu -hostname=xxxx-xxxx.eu.ngrok.io 80All set but even after starting the tunnel, I could not access the content from the vulnerable website, i.e index.html
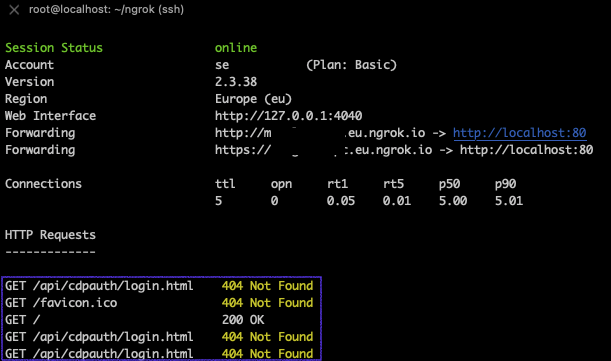
Looking at the Ngrok traffic/incoming request I got to know that the default page was
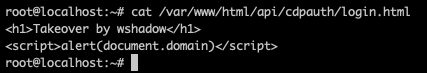
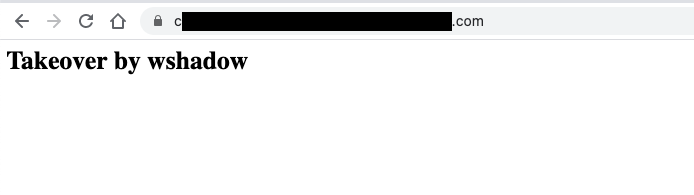
/api/cdpauth/login.htmlI was amazed by this behavior, the tunneling is working for sure but the index page on the localhost is not accessible because the default path hit is different, But why so ??? so I created a similar path in my server and hosted content.
In order to make it accessible even after I shut my laptop, I chose to run ngrok in my Virtual Private Server in the background using “nohup” command.
And here we go.
Reward: NO NO NO
Note: You need to subscribe to Ngrok Subscription for verifying the issue.