With the rapid growth of technology, the mediums of data transfer are in copious amount. Whether they are an analog, classic or digital method all do have traces which can be used to figure out the mechanism of their working.
Let’s forget about the Semiconductors, Magnetic Storage Devices, and Superior wireless technology.
Imagine if we could carry data with our human body without any digital equipment or physical devices. Forging the information in a cyber world like a digital thieve, fooling security devices as well as manipulating human brains with primitive but smart technology. Wouldn’t that be cool enough?
Medical science and Biotechnology has progressed a lot in the last decade outcoming astonishing results relating with information and technology.
We heard of Japanese researcher storing data in the fish brain for a flash drive. (Not sure of this)
“Fish brain USB flash drive” it sounds cool, isn’t it?
Heard about Storing data in DNA?
where one gram of DNA can potentially hold up to 455 exabytes of data
Where 1 Exabyte= 1 billion Gigabytes
It is believed that by the year 2020 AD the total amount of data in the world will reach to 44 zettabytes, where 1 zettabyte = 1000 exabytes
Which means 97.77 gram of DNA would be plenty enough to store the entire data of the world.
Never mind! these kinds of stuff might seem theoretical, ideal or abstract only. lets put some sprinkles of cyberpunk or real-world scenarios at the topic of mediums of Information forging or smuggling the data secretly.
I thought to write this post a few months ago somehow the clock didn’t favor or that thought didn’t come in my mind which may have suppressed me to write this early.
We pass through the airports, security checks, or even at the workplace where employees are neither allowed to bring nor to take any kinds of digital equipment’s like USB, Magnetic devices, everything that resemble the medium of data transfer.
How cool it would be to carry data without semiconductors, without even a piece of paper, without even memorizing it, Completely like Mr. Robot way?
I believe there wasn’t something regarding data stealing without digital equipment in the movies though.
This is a true accident happened with me.
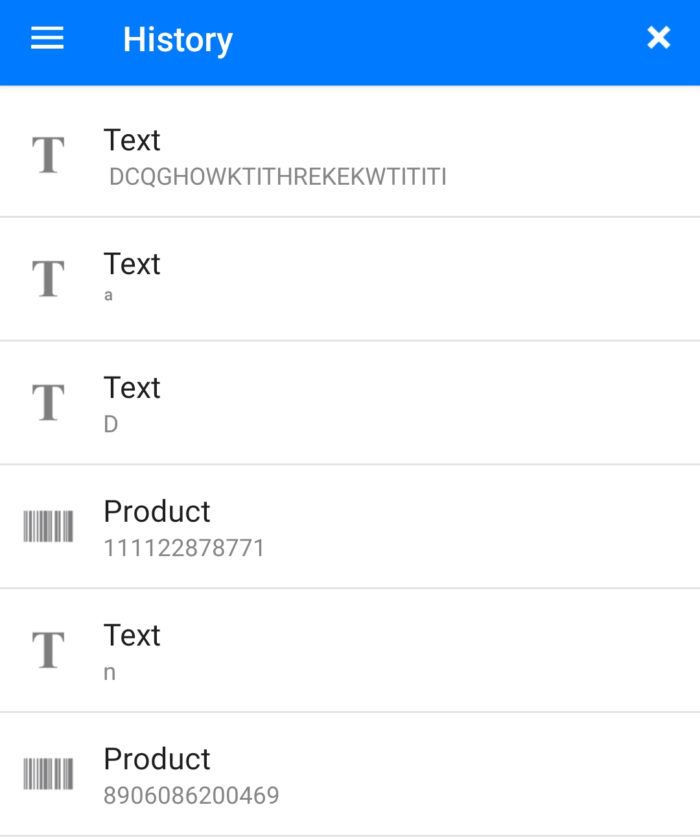
It was a regular evening at my workplace with my laptop on the work desk and I picked up my phone to scan a bar code residing on a bottle of a cold drink which I bought from a supermarket. As soon as I launched a barcode scanner app from my phone I flipped the phone towards me in order to scan the QR code.
I picked the can of my soft drink but before scanning the product the Barcode scanner showed me a scanned result.
I was like wholly amused with it I even didn’t scan the product, and it gave me results like really how?
It took me a few seconds to discover that it was my shirt yes I prefer formal shirt, and it was white stripes on black or black on white whatever you call.

And I got amazing barcode scan results when I attempted to scan a few more times.
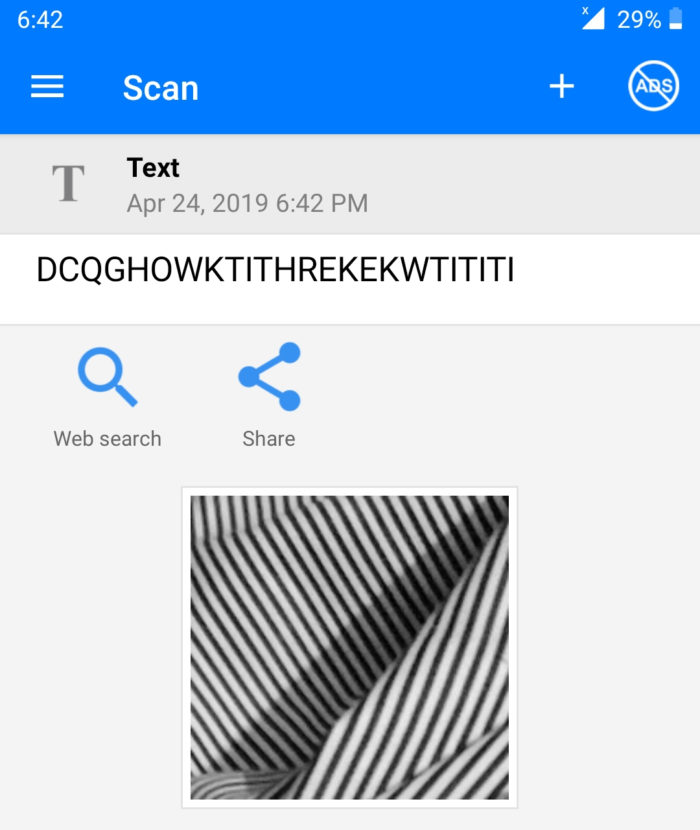
I made a few more scans it was discovered that the scanner was mostly getting random data without any pattern. Just because the barcode or the printed pattern on my shirt was didn’t mean anything.
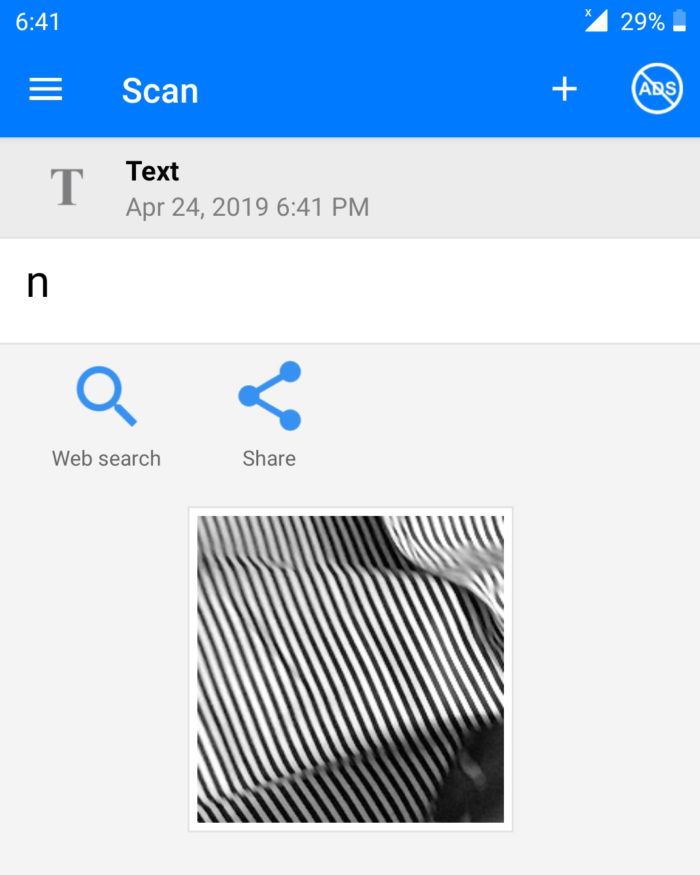
Some of the quick and random scans are reflected below.
It happened, and I thought this is amazing, Travelling without any digital types of equipment, devices, but carrying a lot of information with your clothes sounds pretty cool.
I could have posted it in facebook for fun for a few hours or days, but I thought to exploit it beautifully.
And of course, I shared it with Kailash primitively, I thought it in all possible way.
Being infosec learner i thought how about giving it a shape of security protocol or a cool way to forge information.
And I got a tip from Kailash that it can be used in our daily life an example of an Applied Hacking?
I booted my Raspberry pi 0 (a tiny $10 computer) installed open cv and of course, ironed my Barcode printed Shirt 😀
I setup zbar and simpleCV created a python script that scans a QR code and prints the data. I wanted to chain the trigger to the Jenkins process and perform ……………………………….
To be continued… 1/3
It’s an amazing read . I look forward to remaining parts.
Very good sir. I am really impressed with your re-search. Can we make a custom t-shirt fully printed with bar-codes and go every where wearing, will some one stop us(Security Personnel)
Yes of course thats what Part 2/3 is related with. Keep visiting.
-Thanks
I found a new thing today from you
Glad to hear.